How Does File Deletion work in Linux


Although we create,delete, modify a number of files on the system everyday, the system does a lot of operations behind that simple thing to work. There are different operations done by the operating system, on the file system, whenever a file is deleted or created. I have tried to explain the main data structure behind files called inodes, in my post Inodes and its structure in Linux
In this post we will be covering and comparing the below things.
- How a file is deleted in ext2 Filesystem
- How a file is deleted in ext3 Filesystem
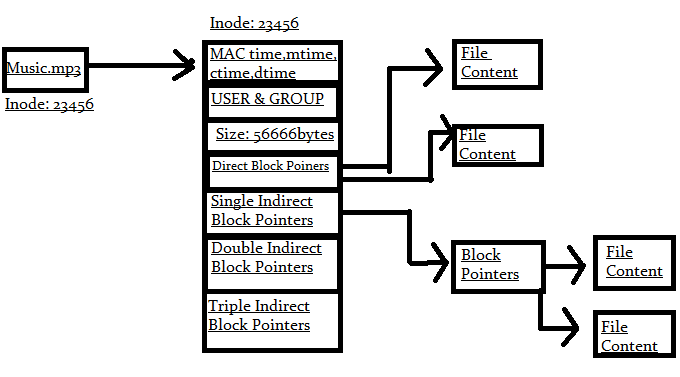
In the above shown diagram i have shown the inode structure of the file music.mp3 and how data block address are linked with the help of direct block pointers and indirect block pointers.
Direct Block pointers point to the blocks where the data is located. Whereas indirect block pointers will point to the blocks which willl intern point to the blocks where data is located. Direct block pointers are inside inode content and stores the block address of the data in itself. But indirect,double indirect, and triple indirect block pointers are just pointers pointing to the blocks which inturn point to data blocks, Which is evident from the above figure.
We will be comparing how the inode gets modified by its structure whenever the file music.mp3 is deleted.
What happens to the inode when a file is deleted in ext2?
Lets see what happens to the structure of the inode if the file music.mp3 is deleted.
And imagine that we are currently working in ext2 filesystem.
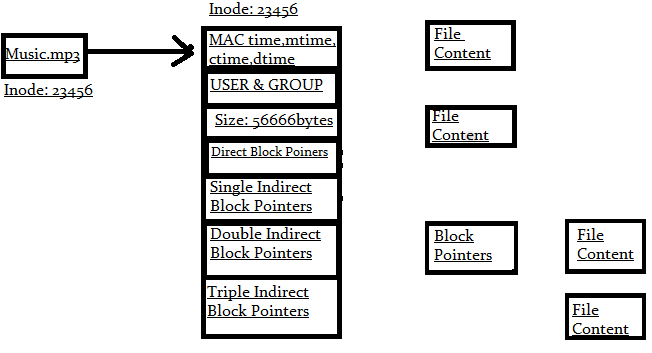
You can clearly see from the above figure that the inode, its structure and the block pointers are still there. But the inode and the blocks where the data is stored are just marked as unused so that this inode number and data blocks can be reused.
So you can easily recover the data, with just the information contained in the inode structure.
We will be discussing the tools for data recovery of individual files in one of our upcoming posts.
icat tool can be used for recovering files, that are deleted and can be done very easily if the blocks are not rewritten. This is the reason why people suggest unmounting the filesystem as soon as some a file is deleted and you want to recover it.
What Happens to the inode when a file is deleted in ext3?
Now lets again delete that same music.mp3 file in ext3 filesystem and see how the structure of the inode changes. Ext3 file system handles file deletion very differently than the ext2 file system.
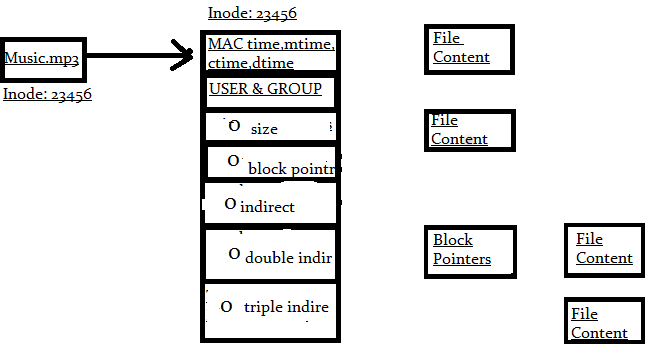
Now you need to note the fact that in ext3 filesystem whenever you delete a file, the size,block pointers(direct,indirect,double indirect,triple indirect) are made zero by the operating system. This process of zeroing the fields in an inode in ext3 filesystem makes data recovery part a bit more tricky.
Due to zeroing of size, and block pointers in inode, the user cannot accurately detect the starting block of a data, and ending block of a data.
[root@slashroot1 ~]# istat /dev/sda1 3470028 inode: 3470028 Not Allocated Group: 106 Generation Id: 1712167956 uid / gid: 0 / 0 mode: rrw-r--r-- size: 0 num of links: 0 Extended Attributes (Block: 3474438) security.selinux=root:object_r:user_home_t:s0 Inode Times: Accessed: 2012-11-12 18:42:48 (IST) File Modified: 2012-12-03 14:07:49 (IST) Inode Modified: 2012-12-03 14:07:49 (IST) Deleted: 2012-12-03 14:07:49 (IST) Direct Blocks:
The above shown example is the istat output for a deleted file. You can clearly see that the size,num of links,uid & gid are all set to zero and also the inode number is set to unallocated.
I have used the istat utility from TSK tools for the above output. Which is an intersting tool for forensic analysis(I will be doing a dedicated post on TSK tools).
Still if you have the inode number available of the file deleted, You will be able to recover the file.(you can get the inode number from the journal of the filesystem.)
Hope this post was helpful in understanding the structure of inode after file deletion.


 Sarath Pillai
Sarath Pillai Satish Tiwary
Satish Tiwary
Comments
what about ext4?
what about ext4?
What Happens to the inode when a file is deleted in ext4?
query
I wanna know how we can retrieve a deleted file in linux if iam using ext4 filesystem kindly reply..Thanks in advance
Add new comment